ENDPOINT PRIVILEGE MANAGEMENT AND APPLICATION CONTROL SOFTWARE
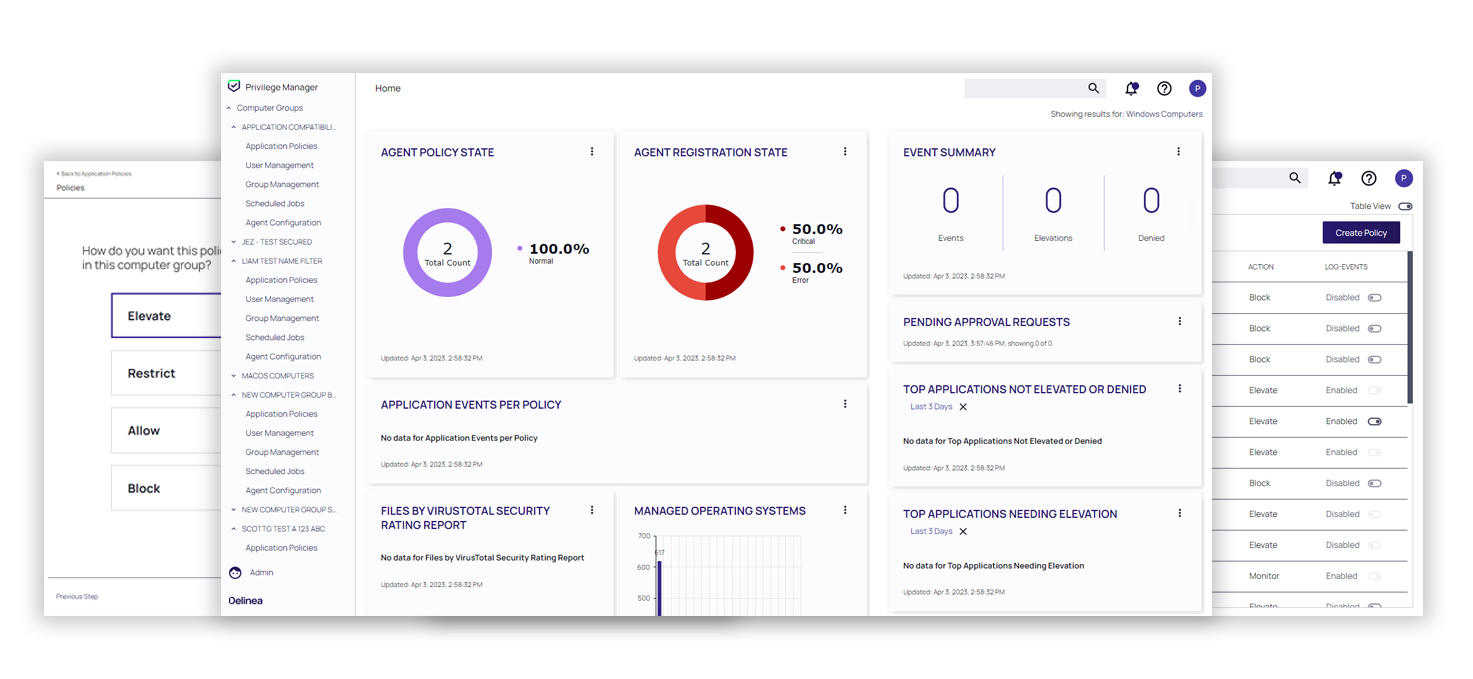
Privilege Manager
Mitigate malware and modern security threats from exploiting applications by removing local administrative rights and enforcing least privilege on endpoints
Enterprise-scale cloud endpoint privilege management at lightning speed
Get started quickly
Deploy across hundreds of thousands of machines with a cloud solution. Take advantage of Privilege Manager for workstations and Cloud Suite for servers.
Secure endpoint access
Discover machines, accounts and applications with admin rights, for workstations and cloud hosted-servers, and automatically apply policies to manage privileges.
Stay in compliance
Report on application usage blocked malware and least privilege compliance. Take advantage of Privileged Behavior Analytics integration with Privilege Manager Cloud.
Mitigate critical vulnerabilities without disrupting business users or your IT support team
Privilege Manager is Delinea's endpoint privilege management and application control solution for workstations.
See how Privilege Manager lets you…
Deploy a single agent
Discover applications with admin rights, even on non-domain machines, and apply policies.
Define flexible policies
Elevate, allow, deny, and restrict applications in just a few clicks with a policy wizard. Easy creation of the first policies with The Workstation Policy Framework.
Manage / remove local admin rights
Create rules to permanently define local group membership and automatically rotate non-human privileged credentials.
Elevate applications
Allow trusted applications to run, block or sandbox others, all while maintaining a least privilege model. Strengthen Windows and Mac application elevation security with MFA, improving access control and identity verification.
Improve IT & end-user productivity
Helpdesk tickets decrease with automated bulk or repeatable operations; people automatically access apps and systems they need.
Check out our interactive demos to experience these capabilities yourself
Try Privilege Manager
Privilege Manager’s practical software features are among the many reasons cybersecurity professionals and IT Admins consider it the best cloud-based endpoint privilege management solution on the planet.
Features |
|
|
Discovery |
|
|
Local Security |
|
|
Application Control |
|
|
Auditing and Reporting |
|
|
Integrations |
|
|
Enterprise Readiness |
|
Download Privilege Manager datasheet for more information, or view the features list.
Try on-premise or in the cloud for 30 days free
Privilege Manager supports extended PAM
The standard definition of PAM isn’t sufficient for the growing risk of cyberattacks. We believe PAM must address the exploding number of identities and today’s IT complexities.
Our products provide effective authorization controls for an identity-centric approach to security.
Privilege Manager
Cloud
Enterprise-grade PAM-as-a-Service to support large enterprises and fast growing organizations at scale.
Privilege Manager
On-Premises
Intelligent PAM to meet cyber security and least privilege best practices and compliance obligations.
Least Privilege Cybersecurity for Dummies
The smart guide to jump-start your least privilege strategy. Get this free 16-page eBook to see how you can limit user and application access to privileged accounts—especially on endpoints—through various controls and tools without impacting productivity.
Least Privilege Discovery Tool for Windows
Do you know which accounts are overprivileged? With Delinea’s Least Privilege Discovery tool, you’ll save time planning your least privilege strategy with critical insight into your vulnerabilities.
