Key takeaways from the 2021 Cyberthreat Defense Report

Barbara Hoffman
The recently released Cyberthreat Defense Report (CDR) 2021 from CyberEdge Group is packed with information about the rapidly evolving cybersecurity universe in the wake of a global pandemic. Now in its eighth year, the 2021 CDR assessed the views of 1,200 IT security professionals representing 17 countries and 19 industries. It is one of the most geographically comprehensive views of IT security perceptions in the industry and Delinea (formerly Thycotic) is proud to be a sponsor.
The report details several key insights worth highlighting:
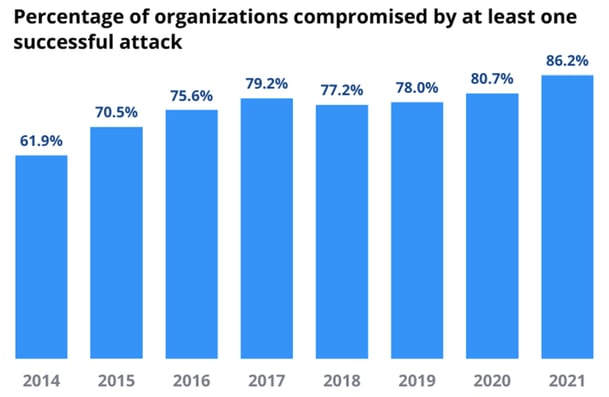
- A record-high 86% of organizations suffered from a successful cyberattack last year
- A record 69% of organizations were compromised by ransomware last year
- 57% of ransomware victims paid ransoms and 72% recovered their data bolstering cyber criminal cryptocurrency accounts
- Malware, spear-phishing, and ransomware cause the most headaches while zero-day attacks are of least concern
BYOD makes securing mobile devices the top challenge
In the wake of a dramatic rise in bring-your-own-device (BYOD) policy adoptions stemming from the global shift towards remote work, survey respondents rated mobile devices as the most challenging IT component to secure. The number of organizations with BYOD policies, for example, jumped nearly 60% due to the near-instant increase in remote workers. These mobile devices were mostly, if not almost entirely, unmanaged with little or no security protections.
Approximately nine out of ten organizations (91%) have been affected by cyberattacks targeting web and mobile applications. Of the five most common types of web and mobile application attacks, respondents ranked their biggest concerns.
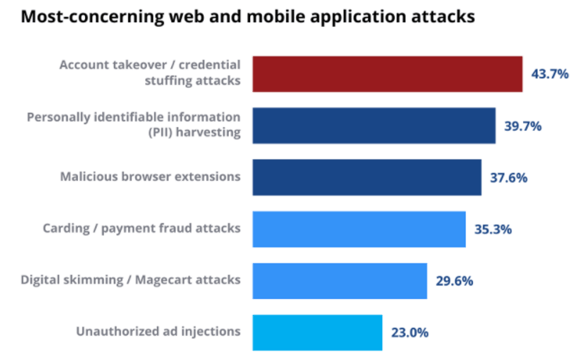
At the top of the list were account takeover attacks (43.7%), which rely on a technique known as “credential stuffing.” This is an automated attack that uses breached username/password pairs to fraudulently gain access to user accounts.
Step 1: The attacker acquires usernames and passwords from the dark web following a website data breach.
Step 2: The attacker uses an account checker to test the stolen credentials against various social media and/or online marketplace websites.
Step 3: Successful logins (usually around 0.1% to 0.2% of total login attempts) allow the attacker to take over the account matching the stolen credentials.
Step 4: The attacker exfiltrates credit card numbers and other personally identifiable information (PII).
Cybersecurity priorities and spending shift
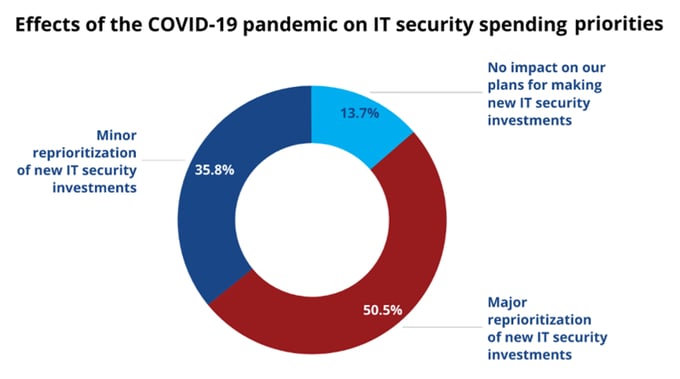
According to the report, seven out of eight organizations (86.3%) recalculated their cybersecurity spending in 2020 because of the COVID 19 pandemic, with just over half (50.5%) saying the pandemic triggered a major re-prioritization of new IT security investment. Organizations surveyed changed their IT security spending priorities to help secure the “massive” increase in remote workers, to control the expanding set of unmanaged personal devices, and to cope with the accelerated increase in cyber threats and other security risks.
- 114% average increase in remote workers
- 59% increase in BYOD policies
- Insufficient remote access capacity
- Huge increase in cyber threats and security incidents
Password management/automated reset topped the list as an important component of most identity access management (IAM) strategies for saving valuable IT administration cycles and improving user experiences. Privileged account/access management (PAM) followed closely, helping organizations prevent insider attacks and unauthorized privilege escalation while enforcing principles of least privilege.
For technologies currently in use or planned for purchase, advanced security analytics equipped with machine learning (ML) and/or AI threat detection engines jumped from last place in 2019 to second place in 2020. This year, it remains in second place as one of the top cyber threat hunting solutions in the industry, while security configuration management remains a top contender for the third consecutive year.
Organizations also put endpoint security near the top of their technology shopping lists, with deception technology, browser/internet isolation, and advanced anti-malware technologies as the endpoint security technologies most sought after.
One key takeaway from a budget standpoint: overall IT security spending is still rising, but at a slower pace than in the past. For the first time since CyberEdge started tracking it, the percentage of a typical IT budget spent on security remained flat at 13% rather than increasing. And for the first time ever, the percentage of organizations with rising security budgets fell from 85% to 78%, and the average security budget increase also declined from 5% to 4%.
Pandemic accelerates cybersecurity moving to the cloud
Not surprisingly to anyone, the COVID-19 pandemic has sparked more interest in cloud-based IT security solutions than ever before, according to the report. These days, 41% of security applications and services are delivered via the cloud, up from 36% last year—that’s a 14% increase in just 12 months!
Biggest defense inhibitors
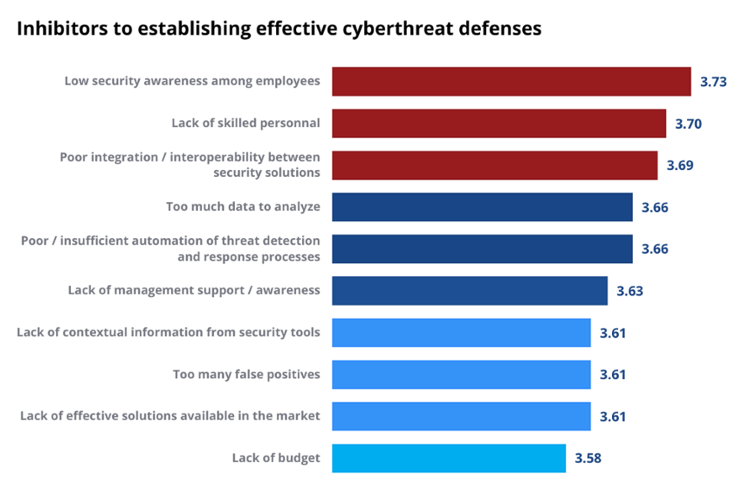
Results from respondents rated low-security awareness among employees and lack of skilled personnel as their top two barriers to defend their organizations against cyberattacks. Third was poor integration/interoperability between security solutions, up from the number six position last year and the highest jump in rating changes. As the report noted, “Nobody wants security solutions that work in isolation. The best security solutions share intelligence and/or perform functions with other security solutions, even if they are provided by different vendors.”
Not if, but when…
The Cyberthreat Defense Report for 2021 strikes a cautionary note for all of us IT professionals with one of its major takeaways. Pessimism among IT security professionals doubled over the past year and is now the new normal, according to the report. For the first time, three-quarters of 76% of security professionals believe a successful attack is imminent—that’s up from only 38% seven years ago.
At the same time, the report suggests IT security professionals are no longer just measured on their abilities to prevent cyberattacks from happening, but on their success in detecting, terminating, and remediating in-progress attacks. This last finding points to the importance of developing and testing your own Incident Response Plan. Delinea has two great resources that can help in that category. Check out our Incident Response solutions page, and download our free Incident Response Plan Template.
Again, you can download the complete 2021 Cyberthreat Defense Report here.

FREE TOOL
Cybersecurity Incident Response Template



