IT onboarding checklist

Alex FitzGerald
An effective onboarding process is critical to the successful integration of new employees into an organization. IT onboarding involves more than just introducing new hires to their colleagues and workspace, it must also include hardware and software setup, security protocols, communication and collaboration tools, and employee training.
Cybersecurity risks need to be given priority in the IT onboarding process to ensure safety for all employees. Without proper onboarding standards in place, new employees may feel overwhelmed or set up to fail and the organization may be at risk of significant cybersecurity threats.
This blog post covers best practices for secure and seamless new hire onboarding, with an IT onboarding checklist to help you get it right.
Hackers say that the fastest way to breach a company’s security controls is through an employee
Knowing what we do about cybercrime today, there should be no employee onboarding plan that does not include a pre-orientation IT onboarding checklist. This is where the IT department prepares in advance for the new employee’s secure introduction to the network.
Why automate the onboarding process?
Implementing automation in IT onboarding improves company security by reducing the chance of human error and ensuring each step is implemented efficiently. Creating automated onboarding workflows based on your checklist is an excellent way to ensure IT onboarding happens as desired by your organization and your new hire.
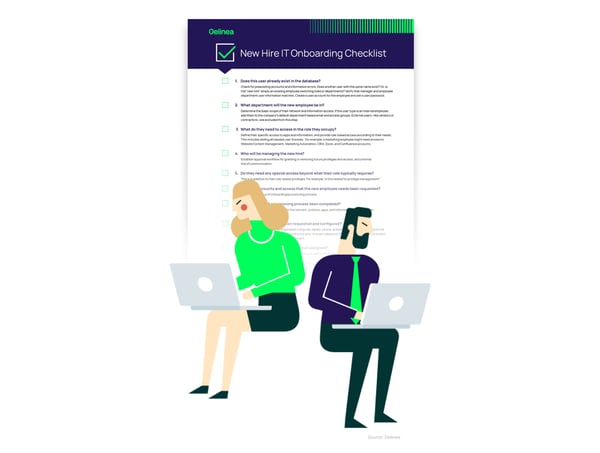
IT onboarding checklist:
1. Does this user already exist in the database?
Check for preexisting accounts and information errors. Does another user with the same name exist? Or, is the “new hire” simply an existing employee switching roles or departments? Verify that manager and employee department user information matches. Create a user account for the employee and set a user password.
2. What department will the new employee be in?
Determine the basic scope of their network and information access. If the user type is an internal employee, add them to the company’s default department-based email and access groups. External users—like vendors or contractors—are excluded from this step
3. What do they need to access in the role they occupy?
Define their specific access to apps and information, and provide role-based access according to their needs. This includes adding all needed user licenses. For example, a marketing employee might need access to Website Content Management, Marketing Automation, CRM, Zoom, and Confluence accounts.
4. Who will be managing the new hire?
Establish approval workflow for granting or removing future privileges and access, and a formal line of communication.
5. Do they need any special access beyond what their role typically requires?
This is in addition to their role-based privileges. For example, is this related to privilege management?
6. Have the accounts and access needed by the new employee been requested?
Monitor the status of the onboarding/provisioning process.
7. Has the account provisioning process been completed?
Create new accounts for access to the network, systems, apps, and information required for the new hire to do their job.
8. Have physical IT assets been requested and configured?
Assets include items like the employee’s computer, laptop, phone, and key fob for physical access to the workplace. Account provisioning should occur prior to asset release so that new hires can log in and start working as soon as they have their equipment.
9. Has mandatory security training been assigned?
Add your new hire to mandatory security training, as well as other required training.
10. Has follow-up occurred to confirm the new employee has access to everything they need to perform their role?
11. Email your stakeholders—including the manager, HR, Apps, and Helpdesk team—about the new employee’s provisioning success.
Download the IT Onboarding Checklist
If any of the questions on the checklist are not answered during the onboarding process, improper access could be granted. It is important for Human Resources, Security, and IT to work together to create a repeatable, auditable, and automated process to ensure accuracy. If the new employee will work in a key function that requires access to sensitive or privileged accounts, it is even more vital that this process be monitored.Why is a systematic onboarding process necessary?
Remember when the VP of Information Technology for the Alberta Motor Association defrauded the company of $8.2 million over a three-year period? He was the only individual with authority to approve payments, so he would submit fraudulent invoices and then approve them. That is a segregation of duty violation. This should have been caught during an access review. This is just one example of how improper onboarding can cost a company millions.
Let onboarding and orientation begin—securely
99% of cyber criminals say tactics like phishing are still effective.
With the pre-orientation IT onboarding checklist taken care of, orientation can begin. Depending on your organization, the current process may take hours or days. I recommend allocating at least a day to the process because a robust employee onboarding program must include a well-delivered Cybersecurity Awareness Training Program.
One thing that new employees may be bringing into your organization are poor cybersecurity practices. Your training program should not be “Death by PowerPoint” but be engaging, informative, and ongoing.
50% of employees haven’t changed their social network passwords for a year or more
The failure statistics around employee cyber hygiene are unnerving. Cybersecurity awareness training for employees is critical, and it must start on their first day in the workplace. Orientation not only provides the new hire with an opportunity to familiarize themselves with your network and cybersecurity best practices but also allows you to assess them as a cybersecurity risk.
Cybercriminals target everyone from an intern to a CEO with equal success. So cybersecurity is everybody’s responsibility, and this point should be emphasized on day one.
What does cybersecurity like this cost? Not as much as you think




