Cloud Security Best Practices Checklist

Barbara Hoffman
Transitioning to the cloud is one of the most significant technology shifts your company will face. Over 80% of organizations operating in the cloud have experienced at least one compromised account each month, stemming from external actors, malicious insiders, or unintentional mistakes.
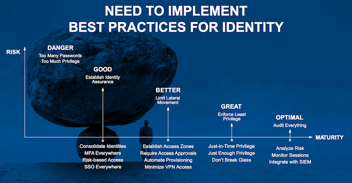
The specifics of cloud security activities may vary depending on your cloud platforms and use cases, however, there are some best practices that every organization should follow. We’ve learned many of those practices from helping thousands of businesses plan, design, and build their cloud PAM programs.
Our PAM cloud security best practices checklist detailed below will help you prevent your organization’s privileged accounts from being compromised and ensure security controls are in place to mitigate the risk of a successful cyberattack. Forward this checklist to your IT Security Team!
Cloud Security Best Practices Checklist
Best Practice #1. Map compliance requirements to cloud functions
Compliance isn’t the ultimate goal of cybersecurity, but it’s an important step to protecting your cloud resources, so it’s #1 on our cloud security checklist. Map your Privileged Access Management (PAM) policies to any compliance mandates that are required for your business. Whether you follow NIST, CIS Controls, or another best practice framework for cybersecurity, make sure you include cloud protections in your policies. Document your PAM policies and share those policies with anyone who may interact with privileged accounts.
Best Practice #2. Establish a Cloud Business Office
Some of the most successful organizations we work with, especially those that have adopted a cloud-first vision, create a Cloud Business Office (CBO). In this best practice model, the CBO has broad visibility and oversight over all cloud activities. They serve as a central point for decisions, communications, and project management to ensure that corporate or government policies and best practices for cloud security are being followed.
The CBO may sit within the IT department, but it actually represents a cross-functional team. It’s a great way to organize your stakeholders across departments, including cloud architects, cloud engineers, developers, operations, security teams, compliance/risk managers, and business owners that have an impact and perspective on cloud usage and strategy.
The Cloud Architect Alliance organized an event about the Cloud Business Office and posted several videos that are worth checking out.
Best Practice #3. Know your cloud security responsibilities
Did you know that the vast majority of cloud misconfigurations and inconsistent controls are the customer’s fault, not the cloud provider’s? AWS and other cloud platforms have many best practice guides they can provide regarding setting up root accounts for servers, configuring S3 buckets, and other settings. Make sure you follow their guidance and have checks in place to ensure all settings are correct.
It’s on your shoulders—not the cloud provider’s—to manage appropriate access and permissions for every person and every system that interacts with cloud-based systems. These systems could include critical applications or databases that are stored in the cloud, cloud platforms for application development, or tools used by your business or technical teams. Cloud access should be incorporated and tracked using the same PAM policies, processes, and solutions you use for your organization as a whole.
Best Practice #4. Implement granular security controls over all types of cloud platforms
Granular cloud access control is one of the PAM best practices many companies fail to achieve. While organizations tend to have broad RBAC in place for cloud infrastructures such as AWS or Azure, they often don’t consider the diverse levels of access involved with web applications.
PAM that is designed for the cloud lets you precisely control what users can see and do in all cloud platforms, including databases and web applications.
Best Practice #5. Don’t make monitoring an afterthought
While the vast majority of users are trustworthy, it’s a best practice to monitor and audit their behavior when they’re accessing sensitive information and privileged accounts. As part of your security program, you should monitor network traffic for unusual activity, such as off-hours access, remote connections, and other outbound activities. Search for telltale signs of compromise by temporarily blocking outbound internet traffic and tracking data outflows.
Even with multiple business and technical functions using different types of cloud resources, with an enterprise-scale PAM solution, it’s possible to have a consolidated view of privileged access across your organization.
Best Practice #6. Take extra care for third parties
Don’t limit insider threat monitoring and oversight to employees. You may be engaging with third-party vendors in a number of ways, such as a remote contractor working on a time-limited project, an embedded contractor, or outsourced staff augmentation.
Vendor security should be practiced both while the third party is actively employed with your organization, and once the engagement is over. Vendor privileged access management (VPAM) solutions can contain the risk, manage privileged access, and provide an audit trail to hold everyone accountable.
Best Practice #7. Never grant standing access
Many companies keep privileges in place for too long, neglect to expire passwords and accounts, and fail to remove privileges when projects end or people leave. Granting standing privileged access violates the best practice principle of least privilege and introduces significant risk.
Implementing Just-In-Time access within Privileged Access Management (PAM) ensures cloud users and systems have appropriate access when needed and for the least amount of time required.
Advanced PAM tools use workflow features such as “Request Access,” which allow users to request access for a specific amount of time. In addition, “Checkout” features can rotate credentials as soon as the checkout period ends, so even if credentials are not expired, a user won’t be able to return with the same credentials.
Best Practice #8. Put your systems to the test
Following a cloud, security checklist gets you far, but without testing, you’re leaving an important question unanswered: is this effort working as expected? Test your cloud security controls to see how well they would stand up to a cyberattack. Many companies bring in ethical cyber criminals or “red teams” to simulate an attack on their cloud systems. This practice can reveal security vulnerabilities before they get exposed by a cybercriminal or flagged in an external audit.
And last, but no less important, Cloud Security Best Practice #9. Plan for change
Last on the checklist but no less important—anticipate change. The average enterprise uses approximately two thousand cloud services, mainly due to SaaS growth. Chances are, your organization has many new SaaS or web applications coming online right now.
If you work in a DevOps environment, new people and systems are continuously accessing your AWS instance or other cloud platforms.
The occasional discovery scan of privileged accounts isn’t going to provide you with the visibility and control you need. Rather, implement continuous discovery for all types of cloud accounts as a best practice. Then you can make sure permissions are properly configured and appropriate oversight is in place.
To match the expected growth of your privileged accounts, cloud applications, and users, it’s best to use a cloud-based PAM solution. Cloud PAM gives you the ability to scale without slowing down other resources or losing control.
In DevOps organizations, where a broad range of cloud resources are continuously created, used, and retired on a large scale, PAM automates high-speed secret creation, archiving, retrieval, and rotation.
Learn more about security for PAM for cloud-based systems
- Get the eBook: Critical Controls for Modern Cloud Security
- Read the blog post: Shadow IT Security Risks: Web applications off your radar make privileged access management even more complicated
Get a quote for the easiest-to-use enterprise-grade PAM solution available both in the cloud and on-premise