Top 10 Cybersecurity experts to follow on social

Jordan True
Feel like you’re experiencing cyber security overload?
As a cybersecurity expert, you must stay ahead, but it can be hard when there is so much noise. And it’s not like you can turn a blind eye—your company is relying on you to keep everything operating efficiently. And if that’s not enough pressure, you are responsible for keeping everything secure and up to code.
Do I have your heart rate rising yet?
Fortunately for you, there are already some brilliant cybersecurity experts who spend their days (and nights) tracking the latest threats, protecting users from cyber criminals, and researching information security and compliance best practices. You can leverage their findings and advice when you need it most, and save yourself a lot of time.
There are cyber security experts who spend their time tracking the latest threats so you don’t have to
So here they are. The top 10 cyber security influencers to follow on social media, in no particular order.
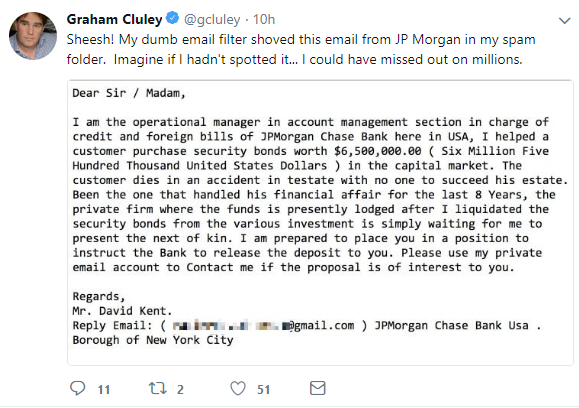
1.) Graham Cluley, @gcluley
Who He Is: Graham has been fighting cyber crime since the early 1990s. Starting as a programmer, he wrote the first ever version of ‘Dr. Solomon’s Anti-Virus Toolkit for Windows’, and in 2011 was inducted into the Infosecurity Europe Hall of Fame.
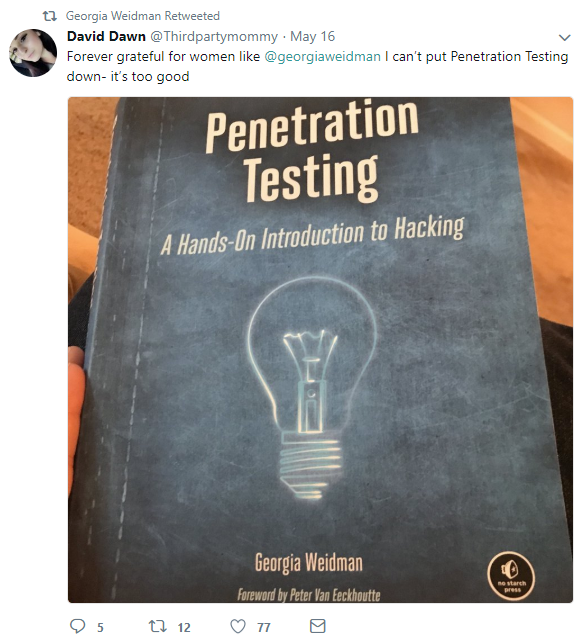
2.) Georgia Weidman, @georgiaweidman
Who She Is: Georgia is a security expert, researcher, and author of “Penetration Testing: A Hands-On Introduction to Hacking”. She spreads her expertise across the world presenting at popular cybersecurity conferences including Black Hat and ShmooCon. Georgia currently works in mobile device security and was awarded a DARPA Cyber Fast Track grant to help support education.
Related post: Check out our choices for the Top 10 Best Cyber Security Podcasts of 2019
3.) Brian Krebs, @briankrebs
Who He Is: Brian spends his days investigating cyber crime as an independent investigative journalist. He launched his career as a reporter for The Washington Post from 1995 to 2009 as the author of the Security Fix blog. What really sparked his interest in cybersecurity was when his entire home network was taken over by a Chinese hacking group. He shares these stories and his interesting experiences on Twitter.

4.) Joseph Steinberg, @JosephSteinberg
Who He Is: Joseph is a cybersecurity thought leader and technology influencer focused on AI and blockchain. He is one of only 28 people in the world to hold all the following security certifications: CISSP, ISSAP, ISSMP, and CSSLP. Joseph offers a broad yet deep knowledge of InfoSec issues on his Twitter channel.

5.) Rebecca Herold, @PrivacyProf
Who She Is: Known as the “Privacy Professor”, Rebecca is an information privacy, security, and compliance consultant. Today she serves on many advisory boards and participates in the NIST standards committee to help create privacy standards for the U.S. Smart Grid. Stay up to date on the latest privacy and data security news by following Rebecca.
What does cybersecurity like this cost? Not as much as you think
6.) Brian Honan, @BrianHonan
Who He Is: Brian has over 25 years of experience as an information security professional. You’ll see him presenting at leading industry conferences including Irisscon, the annual Irish cyber crime conference which he established. He regularly tweets about cyber crime and breaking InfoSec stories.

7.) Joseph Carson, @joe_carson
Who He Is: Joe travels the globe delivering his expertise at the top security conferences. His focus on digital forensics, blockchain, and privileged account management led him to author his book “Cybersecurity for Dummies”. The eBook, which is free, is focused on teaching us how to defend ourselves online and is essential reading for both employees of large organizations and private individuals. Follow Joseph for the latest cybersecurity threats and tips for staying safe online.
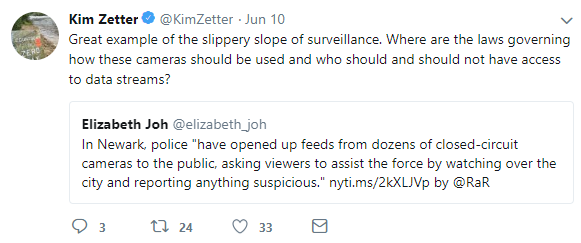
8.) Kim Zetter, @KimZetter
Who She Is: You may have heard of her book “Countdown to Zero Day: Stuxnet and the Launch of the World’s First Digital Weapon” which covers the story behind the virus that disrupted Iran’s nuclear plan. Or maybe you’ve come across her on Wired News where she has written over 100 articles. Her interests include cybercrime and privacy.
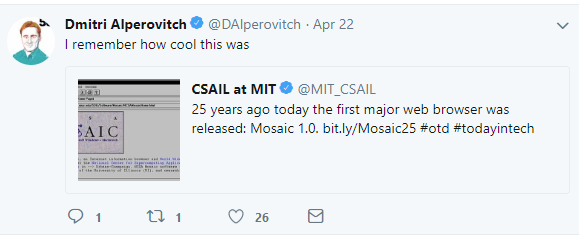
9.) Dmitri Alperovitch, @DAlperovitch
Who He Is: Co-founder and CTO of CrowdStrike, Dimitri has impressive experience working for many computer security startups. In August 2011 Dimitri published, “Operation Shady RAT” which reports on a series of ongoing cyberattacks that hit over 71 organizations including the United Nations. You’ll learn best practices on incident response and breach protection.
10.) Bruce Schneier, @schneierblog
Who He Is: Known as a “security guru” by The Economist, Bruce has incredible experience in the cyber security space and shares his knowledge as the author of over 13 books. You can learn about the top security issues on his blog “Schneier on Security”. He’s been recognized on TV and radio and has testified before Congress. Add him to your Twitter stream so you don’t miss an important security post!





